List all devices on network - cmd command IP scan
The PowerShell commands compiled in this article make it possible to display devices in the local network and usually make special programs for scanning the network superfluous.
Network Scan in PowerShell: List of all network devices
#Foreach all Class C:-Networks (/24)
$(Get-NetIPAddress | where-object {$_.PrefixLength -eq "24"}).IPAddress | Where-Object {$_ -like "*.*"} | % {
$netip="$($([IPAddress]$_).GetAddressBytes()[0]).$($([IPAddress]$_).GetAddressBytes()[1]).$($([IPAddress]$_).GetAddressBytes()[2])"
write-host "`n`nping C-Subnet $netip.1-254 ...`n"
1..254 | % {
(New-Object System.Net.NetworkInformation.Ping).SendPingAsync("$netip.$_","1000") | Out-Null
}
}
#wait until arp-cache: complete
while ($(Get-NetNeighbor).state -eq "incomplete") {write-host "waiting";timeout 1 | out-null}
#add the Hostname and present the result
Get-NetNeighbor | Where-Object -Property state -ne Unreachable | where-object -property state -ne Permanent | select IPaddress,LinkLayerAddress,State, @{n="Hostname"; e={(Resolve-DnsName $_.IPaddress).NameHost}} | Out-GridView
Copying commands to the clipboard
The command block can be easily pasted into the Windows PowerShell console, copy it to the clipboard:
A “right click” in the PowerShell pastes the content and starts the commands:
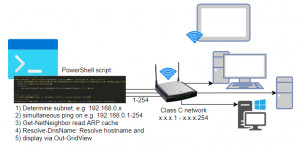
What does the script do in detail?
The ARP cache lists all devices with which the PC has recently had a network connection. For a complete listing of all devices in the local network it therefore helps to contact all possible addresses in advance:
| Ping all devices | Contact all devices on the network using the ping command to fill the ARP cache. |
|---|---|
| Read ARP cache | The command Get-NetNeighbor shows the ARP cache and thus all contacted devices of the local network. |
| Resolve-DnsName | In addition to the IP address, the host name can be added to the device list with Resolve-DnsName. |
| Out-GridView | Out-GridView in PowerShell displays the collected data in an interactive table. |
No software needs to be installed to do this.
The following commands search for all existing class C networks, start a ping on their addresses (1..254) and display the IP addresses contained in the ARP cache including hostname as Out-GridView:
cmd-ping-arp.
Video
In the following YouTube video I show the commands in action:
Background: Network and commands in detail
What is the ARP (Address Resolution Protocol) cache?
Computers that are located in the same IP network - as an example in the subnet 192.168.0.x - communicate directly with each other and do not need a gateway (=router) for this. The unique network addresses of the devices = MAC addresses are used for direct communication. So that the MAC addresses do not have to be queried again and again, these are kept by each device for a certain time in the "ARP cache". The ARP cache lists all IP and MAC addresses of the local network with which the computer has attempted a connection, even if this was blocked by the firewall during the actual connection setup.
How to read the ARP cache with Windows PowerShell?
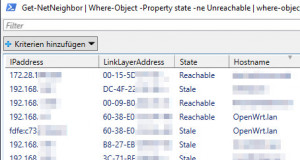
The content of the ARP cache can be read out in PowerShell via the command “Get-NetNeighbor”.
Get-NetNeighbor | Where-Object -Property state -ne Unreachable | where-object -property state -ne Permanent | Out-GridViewIn combination with Out-GridView, the results are output in a window where they can be searched or filtered:
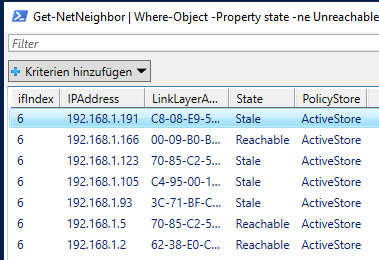
Get-NetNeighbor behaves the same as the arp COMMAND of the command prompt. One way to initiate a connection to a device is to ping it:
Ping to an address
As is known, a ping is used to check a connection to a single computer in the network: ping DESTINATION ADDRESS. It does not matter whether the device is located in the local LAN or in another subnet, i.e. whether it can be reached via the gateway (router). Modern operating systems, such as Windows 10 / 11, block the response to a ping command: ICMP is blocked by the Windows firewall. If the computer is in the same subnet, the IP address is nevertheless entered into the ARP cache in the case of the failed ping attempt, which we can take advantage of. If we try to ping all possible addresses of the subnet, all devices should be listed in the ARP cache.
Ping attempt on all addresses
The above PowerShell commands automatically detect all class C networks (/24 or subnet mask 255.255.255.0) and starts a ping on their addresses: 1-254. Thanks to “System.Net.NetworkInformation.Ping” and “SendPingAsync” the ping runs simultaneously on all devices and the script can very quickly switch to displaying the ARP cache. As already described, it doesn't matter for the filling of the ARP cache whether the computer answers to the ping or not: The main thing is that there is a connection attempt.
To ping a net other than /24, “PrefixLength”, the start and end values: “1..254” and possibly the filling of the variable “$netip” must be adjusted accordingly.
Originally I tested the ping with Test-Connection and Start-Job, the overhead on the part of PowerShell is very high with this. PowerShell consumes relatively much CPU and RAM with Start-Job and Test-Connection and needs about 2 minutes to ping the subnet asynchronously, “System.Net.NetworkInformation.Ping” and “SendPingAsync” however few seconds.
How to read the hostname in Windows PowerShell?
The hostname can be found out with the command “Resolve-DNSName”
PS C:\WINDOWS\system32> (Resolve-DnsName 192.168.1.191).NameHost
LGTV.lanIn the above example, Get-NetNeighbor passes the IP address to Resolve-DnsName and adds it to the display before outputting with Out-GridView.
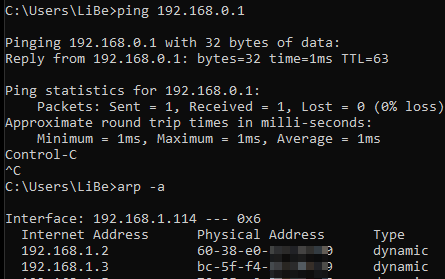
Alternative: Read network addresses in the command prompt
In the command prompt ping all addresses of the complete network with one line?
The ping command can be looped multiple times in the command prompt with the following command line:
for /l %i in (1,1,255) DO @ping 192.168.0.%i -n 1 | find "Bytes="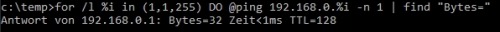
for /l %i in (1,1,255) means: starting from 1 in steps of 1 up to 255
@ping 192.168.0.%i -n 1 .. is the actual ping command (the @ suppresses the output of the command) and by means of
| find "Bytes=" only lines that contain “bytes=", i.e. that respond to the ping, are displayed.
Scan with firewall enabled on local LAN
As an alternative to the PowerShell Get-Netneighbor, the ARP cache can be displayed in the command prompt using arp -a. Since the ARP cache times out for each entry, only new connections are displayed. Additionally, the cache can be cleared with arp -d.
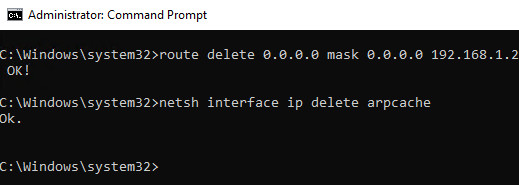
So that all devices are displayed, a “ping” on all devices can be executed in advance again.
The following line in the command prompt starts a ping on all addresses of the complete subnet, waits 10 seconds and displays the ARP cache:
The following command line also lists computers of the local LAN where the firewall is switched on
(for /l %i in (1,1,255) DO start /min ping 192.168.0.%i -n 1) && timeout 10 && arp -a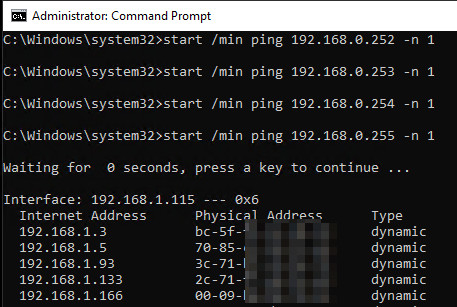
If the computer is in a different subnet, the command line can of course be adapted accordingly:
... in (1,1,255).. ping 192.168.0.%i ....
Legend:
Start and end value for /l %i in (1,1,255) means: starting from 1 in increments of 1 up to 255.
Subnet so everything before the variable (1-255)
Be careful, because start /min starts all 255 pings at the same time: To avoid overloading the PC and the network, the start and end values should not be too large. With the 255 addresses of a class C network I had no problem so far.
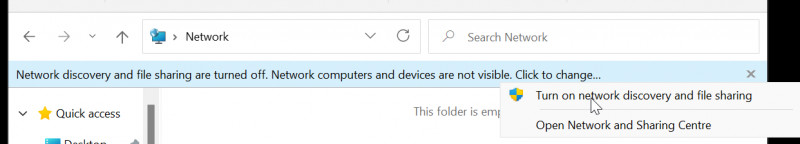
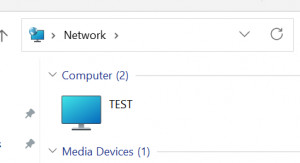
How to display network devices in Windows Explorer?
The easiest way to view devices on the network is to use the Windows Explorer option: “Enable network discovery and file sharing”. Windows 10/11 lists devices in the local network.
By the way, the option can be deactivated again in the control panel:
Control Panel\All Control Panel Items\Network and Sharing Centre\Advanced sharing settings
The network discovery output is not complete because Windows machines with network discovery disabled are not visible to others.
Tools
Special tools provide even more possibilities and a better overview than the Windows board tools. However, depending on the scanner's mode of operation, they provide similar results. Originally I also presented the Angry IP Scanner here, but since it requires JAVA as a prerequisite, I don't want to recommend it here anymore.
Advanced IP Scanner
Special tools provide even more possibilities and a better overview than the Windows board tools. However, depending on the scanner's mode of operation, they provide similar results:
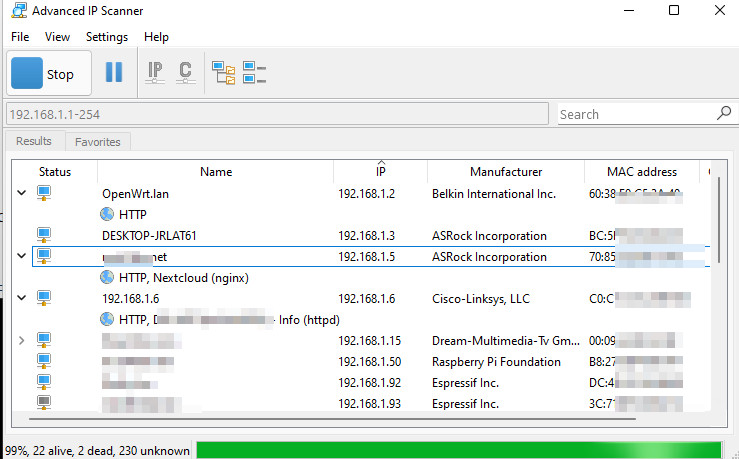
| Program | Advanced IP Scanner |
|---|---|
| current version | 2.5.4594 |
| Manufacturer | http://www.radmin.com/products/ipscanner/ |
| License | Freeware |
The scanner returns similar results as our ARP query, but additionally the hostname and based on the MAC address the manufacturer and information about some services.
Conclusion
The commands presented here eliminate the need to install an IP scanner for a quick overview. A single command line in the command prompt or a handful of PowerShell commands are enough to list all network devices in the local network or in another subnet. However, more comfort and possibly more details are provided by special programs. If you want to take a closer look at a specific device, you can test it for its network services, see: cmd Portscan - Test devices on the network for their services.
 ({{pro_count}})
({{pro_count}})
{{percentage}} % positive
 ({{con_count}})
({{con_count}})