Docker WebHook Daemon: simple hook server for bash scripts
Looking for a solution to be able to receive webhooks from certain systems and trigger certain actions, I came across a very simple Docker container. The container executes simple bash scripts, for this it is enough to specify the script name in the URL and pass appropriate variables via the webhooks.
Webhook: what is it?
Certain systems offer the possibility to add webhooks in their settings. Webhooks are HTTP calls that are executed automatically when certain events occur. For example, if a new commit has taken place on a Git server: In this case, a web server can be informed about the new software release via webhook and the new source code can be activated automatically. This is also the purpose for which I use the Docker image presented here.
Software Webhookd GitHub https://github.com/ncarlier/webhookd current version 1.21.0
found 2026-02-05
Technically, the webhook call is a normal HTTP call, accordingly it could be received and processed by any web server with an appropriate route. Mostly it is possible to distinguish between POST and GET when creating the webhooks, as well as usually an access token can be sent along.
Simple webhook server (webhookd) with Docker
Docker Basics
Docker allows applications to be launched by command in a so-called container.A container is an isolated environment independent of the operating system (OS):
When a container is first launched, Docker independently loads all the necessary sources
from the internet.
Docker can be installed on Windows, macOS or an Linux Distribution
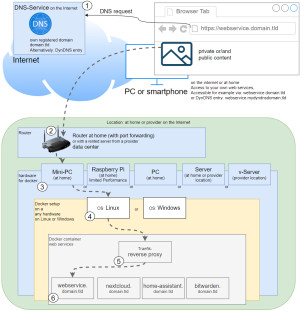
To ensure that webhookd is can be reached securely from the Internet, I use a Let's Encrypt reverse proxy. At first I used Nginx as Reverse-Proxy, but later replaced it with Traefik. The reverse proxy provides an encrypted HTTPS connection and makes it possible to run multiple websites on one server.
Step by step webhookd and Docker including access from the internet
Hardware requirement:- Almost any hardware can be used for the Docker installation. For example, a virtual server of a provider, or for home: a Mini-PC, notebook, MAC, a NAS: QNAP, Synology or any other hardware with x68-64 architecture on which Windows or Linux can be installed.
- Own registered domain, see domain and its management.
- Cloudflare or Reverse Proxy:
- Cloudflare Tunnel Service or alternatively:
- Port forwarding and Reverse proxy with Let's Encrypt certificate
Container for webhookd
- create and customize docker-compose.yml
- start container and
- execute bash scripts
docker-compose.yml
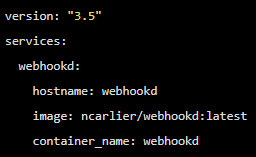
To start the webhook-Container using docker compose, the Docker image can be downloaded, created and started using a simple docker-compose.yml file. The file can be filled with any text editor as follows and then customized:
Filename: docker-compose.yml, Content:
services:
webhookd:
hostname: webhookd
image: ncarlier/webhookd:latest
container_name: webhookd
expose:
- "80"
#For direct test access, remove "#" in the following 2 lines. Call: http://localhost:83 or http://ServerIP:83
#ports:
#- "83:80"
restart: always
environment:
WHD_LISTEN_ADDR: ":80"
WHD_SCRIPTS: /scripts
WHD_HOOK_TIMEOUT: '600'
#Labels for ReverseProxy, see: https://www.libe.net/en-traefik
labels:
- "traefik.enable=true"
- "traefik.http.routers.webhookd.rule=Host(`hook.domain.tld`)"
- "traefik.http.routers.webhookd.entrypoints=web"
- "traefik.http.routers.webhookd.entrypoints=websecure"
- "traefik.http.routers.webhookd.tls.certresolver=myresolver"
volumes:
- ./scripts:/scripts
- /var/run/docker.sock:/var/run/docker.sock
#Without using a reverse proxy (https://www.libe.net/en-traefik) the webproxy network is likely to be missing
#and the following lines can be removed or commented out. Alternatively, the network can be created with "docker network create webproxy".
networks:
default:
name: webproxy
external: trueFor direct access via IP address or localhost - even without reverse proxy, DNS or public IP - the commented out port setting can be activated for test purposes by removing “#“ in front of “ports:” and “-"83:80"“ .
For Internet access via the Traefik reverse proxy, the domain must be replaced in the labels with the previously created DNS entries (in the example:hook.domain.tld).
The example uses bind mounts and not docker volumes to permanently store data. See: Docker data storage: Docker Volumes vs. Host Folders
Start container
Before starting, the scripts folder is still needed. The command docker compose up -d starts webhookd
docker compose up -dsee also: github.com/ncarlier/webhookd
Running bash scripts from a webhook call
After starting the server, any bash scripts can be stored in the ./scripts folder. If the URL of the hook server is called with the script name as path, the Docker container starts the corresponding bash script:
As an example, the following URL: https://webhook.domain.tld/TestBash on the server would invoke a bash script with the same name, i.e.: ./scripts/TestBash.sh.
If parameters are passed during the call, they can be used as variables within the bash script: $Variable. The call in the browser would then be able to pass variables via the GET method as follows: https://webhook.domain.tld/TestBash?Variable=Wert. Those who prefer the use of POST can also pass them using the POST call.
When accessing from a Docker container:
permission denied while trying to connect to the Docker daemon socket at unix:///var/run/docker.sockSolution:
sudo chmod 666 /var/run/docker.sockSo far I have replaced the webhookd container with GitLab and Gitea, and for the signal notification from Grafana has been tested successfully. For GitLab and GitHub a sample script is available, for Gitea I had to create a script myself.
 ({{pro_count}})
({{pro_count}})
{{percentage}} % positive
 ({{con_count}})
({{con_count}})
THANK YOU for your review!
Questions / Comments
(sorted by rating / date) [all comments (best rated first)]